The Zero Trust Hub Editions
Zero Trust Segmentation trends, insights, and resources for today's cybersecurity leaders
My 3 Zero Trust Takeaways from RSAC 2026

Public Sector CTO
It didn’t take long on the RSAC show floor to see where the industry is heading.
You could walk around for five minutes and see AI referenced in just about every direction. It wasn’t limited to one type of solution or one category — it was everywhere.
That level of presence says a lot about where the industry is right now. AI has moved from an emerging concept to something security leaders are actively trying to understand, adopt, and defend against at the same time.
What stood out to me, though, wasn’t just how visible AI was. It was how the conversations around it have matured. Over the course of the week, talking with security leaders across different sectors, there was a clear shift in focus. The questions are becoming more practical, more grounded in execution, and more tied to outcomes.
That shift is shaping how organizations think about Zero Trust today and what they expect it to deliver moving forward. Here are my takeaways from my conversations at RSAC 2026.
1. AI is compressing the timeline for attacks
There’s always hype in this industry, but the pace of change with AI feels different.
One of the most consistent themes I heard at RSAC this year was how quickly attacks are evolving. The gap between when a vulnerability is discovered and when it’s exploited is shrinking fast, and there’s a growing sense that it may not exist at all for long.
That creates a real problem for traditional approaches. A lot of security strategies assume there’s time to react. If that assumption breaks down, then prevention and detection alone won’t carry the weight they once did.
At the same time, there’s an expectation that defenders will use AI to counter AI-driven threats. That’s where some uncertainty comes in. The offensive side is clearly accelerating, and many teams are still figuring out what effective defense looks like at that same speed.
What this really highlights is that AI is taking the problems we’ve had for years and speeding them up. When that happens, limiting how far an attacker can move becomes more important than trying to stop them from getting in.
2. Zero Trust focus has shifted to execution, but the challenging parts haven’t gone away
A year ago, many organizations were still trying to define Zero Trust. That wasn’t the case this year. Most of the conversations I had were about how to actually implement it.
That’s exciting progress, but it doesn’t make things easier.
The same challenges are still there. Budgets are tight, and security teams are balancing competing priorities. Business needs continue to take precedence in many cases. Those realities don’t change just because the strategy is sound.
There’s also a mindset shift happening that’s worth paying attention to. More leaders are openly acknowledging that breaches are going to happen. That’s a realistic view of the threat landscape.
The concern is when that turns into acceptance without a plan. I heard versions of the idea that a breach is just something you deal with when it happens. That kind of thinking removes the urgency around reducing impact.
I think the more productive shift is toward asking how to contain a breach once it occurs. That’s where Zero Trust starts to move from concept to something operational.
3. Segmentation is being tied directly to impact
One of the more encouraging trends this year was how segmentation is being discussed.
The conversation is becoming more practical. Instead of focusing on architecture, teams are starting to focus on outcomes. The question isn’t just how to segment, but what segmentation does for them when something goes wrong.
That usually leads to a practical question: if an attacker gets in, how much of the environment can they actually reach?
Segmentation answers that question. The more effectively you segment, the more you limit lateral movement and reduce the scope of disruption.
I heard more organizations making that connection this year. It’s less about checking a box and more about understanding how to reduce the size of the problem they’ll have to deal with.
Where Zero Trust goes next in an AI-driven world
The pace of change around AI is creating a lot of uncertainty. It’s evolving faster than most organizations can fully plan for, and there are still open questions around regulation, governance, and long-term impact.
What isn’t uncertain is the direction of the threat landscape. Attacks are happening faster, and the pressure on security teams is increasing along with it.
That’s why the focus on containment matters.
You may not be able to prevent every breach, especially as AI continues to accelerate the pace of attacks. What you can control is how far that breach spreads and how much damage it causes once it’s inside your network.
That’s where Zero Trust can deliver. It offers a consistent way to manage what happens next when the initial compromise occurs.
STATSHOT
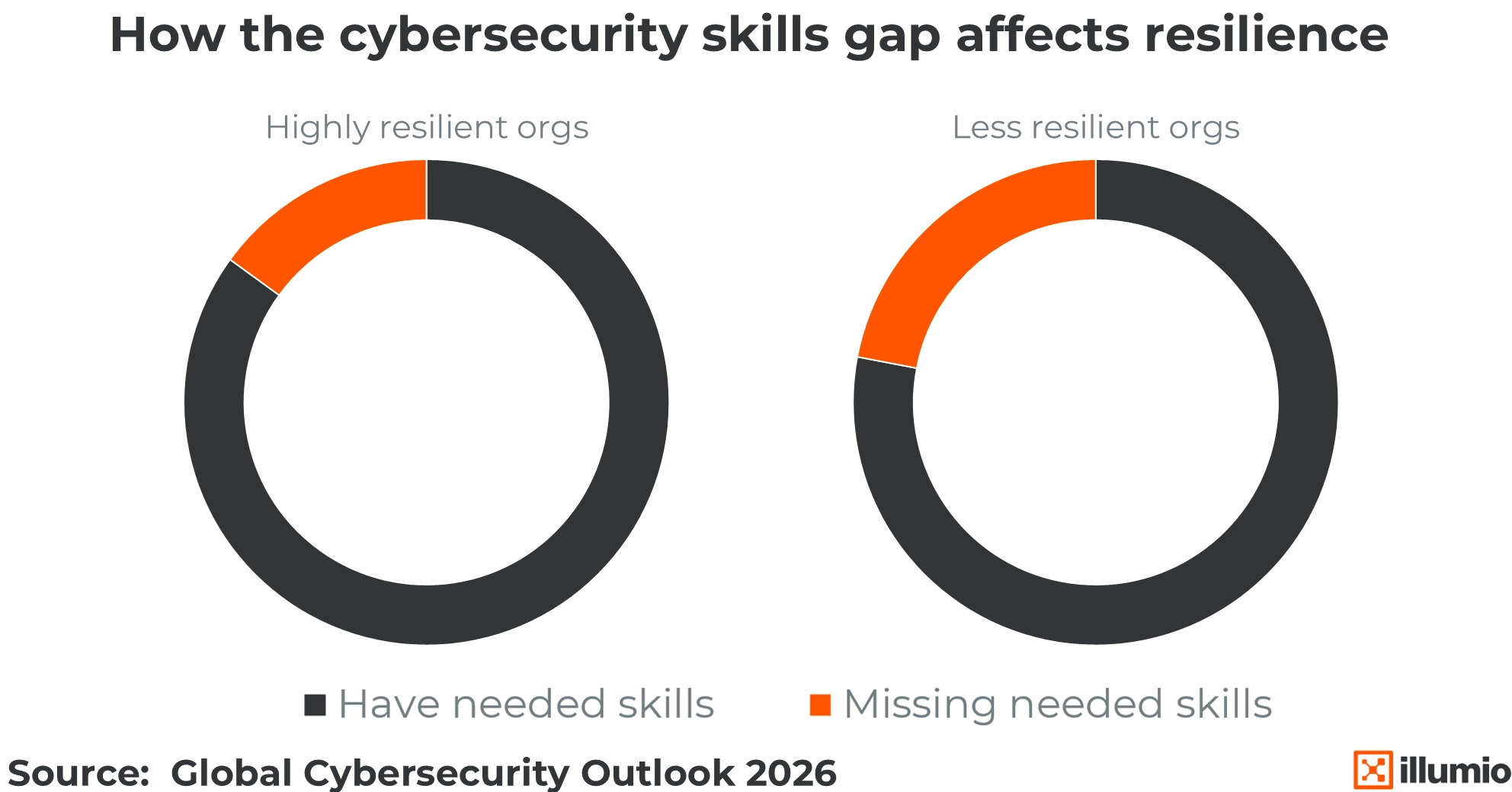
The Skills Divide
Cyber resilience rises and falls with the strength of the team behind it. Organizations with cybersecurity skills gaps say they’re less resilient. But highly resilient ones show a starkly different pattern, with most saying they have the people and expertise they need. When skills are missing, resilience suffers.